How to disable WebRTC and prevent leaks
VPN users beware: Firefox and Chrome have a security vulnerability that may leak your IP address unless you’re using a full-featured VPN like NordVPN. Read on to find out what a WebRTC leak is, how to perform a WebRTC test and how you can protect yourself from vulnerability.
Contents
What is a WebRTC leak?
A WebRTC leak is a vulnerability that can occur in web browsers like Firefox, Google Chrome, Brave, Opera, and others. A WebRTC leak presents a major security risk, as it can expose your real IP address when you’re connected to a subpar VPN that doesn’t protect you against WebRTC leaks.
What is WebRTC?
WebRTC (Web Real-Time Communication) is an open-source tool that allows web browsers to form real-time peer-to-peer connections with the websites they visit.
This allows your Firefox browser, for example, to send live audio and video feeds back and forth between you and another participant online without having to download any additional software. This is a non-proprietary protocol that allows any website to plug in and make such a connection (with your permission).
WebRTC does this by establishing special real time communication channels from the browser. They communicate with the website you’re visiting and exchange information (including your local and public IP addresses).
How does a WebRTC leak happen?
WebRTC leaks happen when communication channels bypass your encrypted tunnel created by using a VPN. In this case websites and online services you visit can see your IP address.
The problem with WebRTC
WebRTC technology presents a massive vulnerability. Any website you visit can potentially request and access your true IP address despite your VPN. When this vulnerability was first discovered, it gave VPN providers (ourselves included) quite a scare. The worst part is that this is part of the basic functionality of WebRTC, so it can’t be “fixed.” It’s up to the user to find ways to block these leaks or disable WebRTC entirely. The good thing is that you can easily perform a WebRTC leak test yourself. Performing the test is one of the best ways to enact WebRTC leak prevention.
How to test for WebRTC leaks
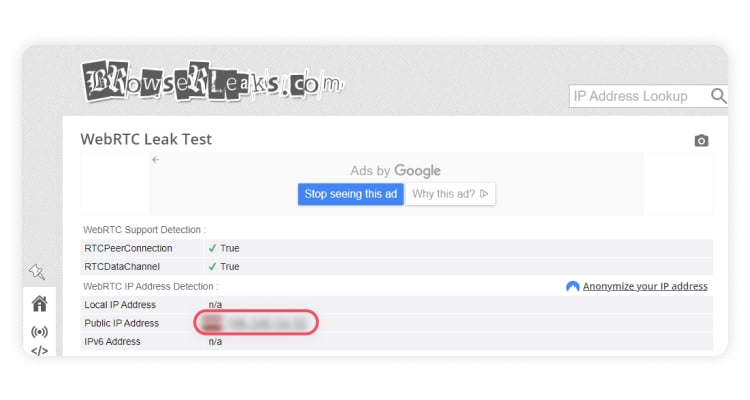
Check your VPN for any potential WebRTC leaks. You can perform a WebRTC leak test by following these simple steps:
- Disconnect and exit whatever VPN you’re using.

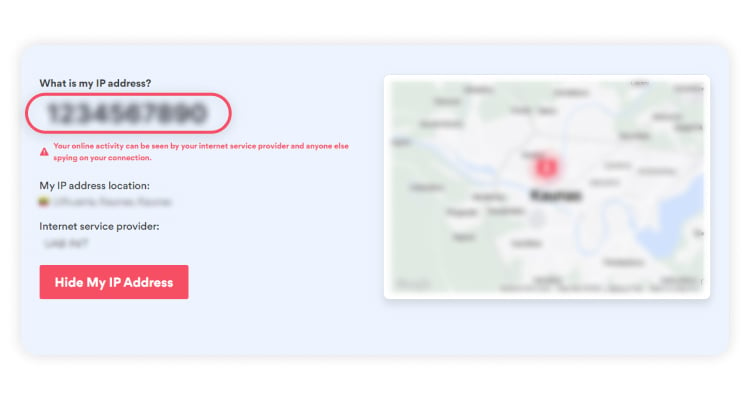
- Check your IP. You can do that by typing “what is my IP” in a Google search. You will see your real IP address, provided by ISP. Note it down.

- Exit the browser.
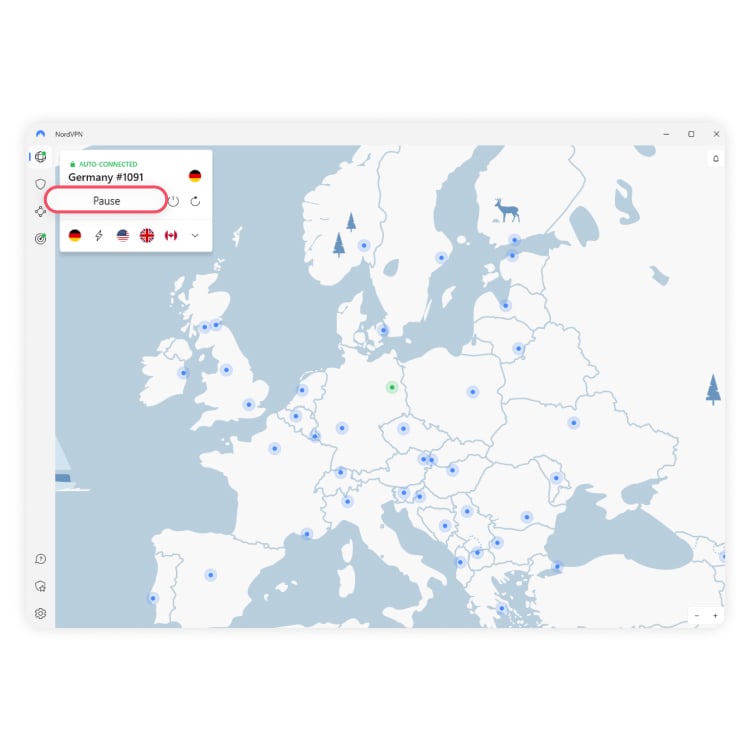
- Re-launch your VPN and connect to a VPN server.

- Launch your browser and visit browserleaks.com.
- Locate WebRTC Leak Test field. If your original IP, the one that you noted down, is not there – you’re good to go.

Note: your original IP usually begins with 10.xxx or 192.xxx or sometimes an alpha-numeric IPv6).
How to block WebRTC leaks
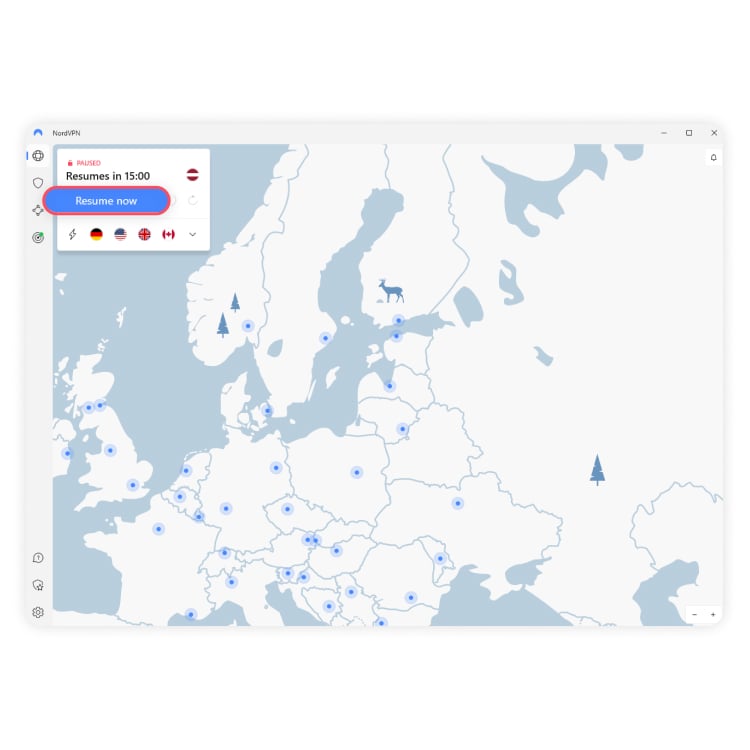
If a WebRTC test showed that there is a leak, there are a few ways to block it. By far the simplest way is to block WebRTC leaks by using NordVPN. Whether you’re using our regular VPN or our browser plugins for Firefox or Chrome, either will block any unwanted IP address leaks through WebRTC while allowing authorized WebRTC connections to continue under your anonymous IP address.
Protect your IP address and enhance online security with the click of a button.
You can also prevent WebRTC leaks by blocking WebRTC requests from your browser, but this process will be a bit more complicated. Furthermore, unlike with NordVPN, blocking WebRTC leaks using these methods will often disable WebRTC functionality completely.
How to disable WebRTC on Chrome
Disabling WebRTC on Chrome is tricky, and we strongly suggest using an extension to do so. That’s because the extension-free way involves manually editing setting files that can potentially make your Chrome browser malfunction if you do it wrong.
WebRTC Leak Prevent is the leading Chrome extension for preventing WebRTC leaks. As the developer has noted, this extension only changes WebRTC’s security and privacy settings – it doesn’t turn WebRTC off.
How to disable WebRTC on Firefox
Fortunately, Firefox does have a built-in way to disable WebRTC. It can be hard to find if you don’t know where to look, so follow these steps!
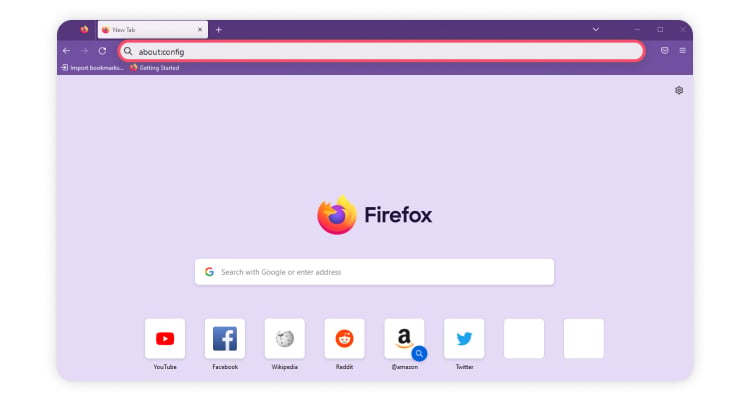
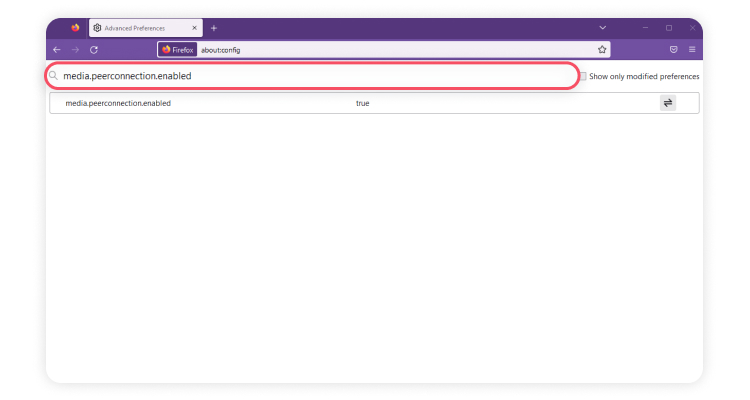
- Write “about:config” into your browser bar and hit Enter.

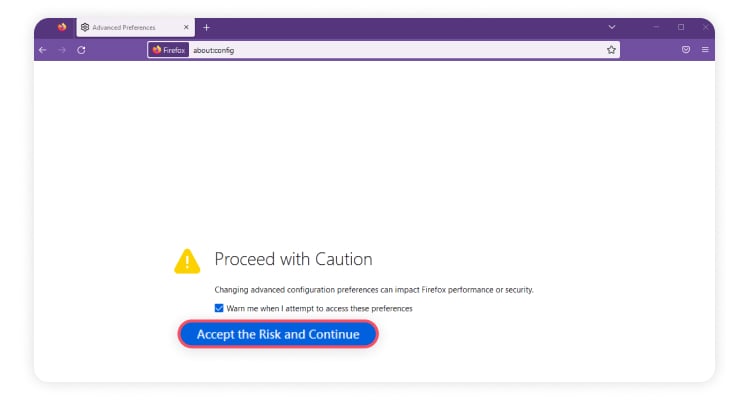
- You will be prompted with a warning. Click on “Accept the Risk and Continue.”

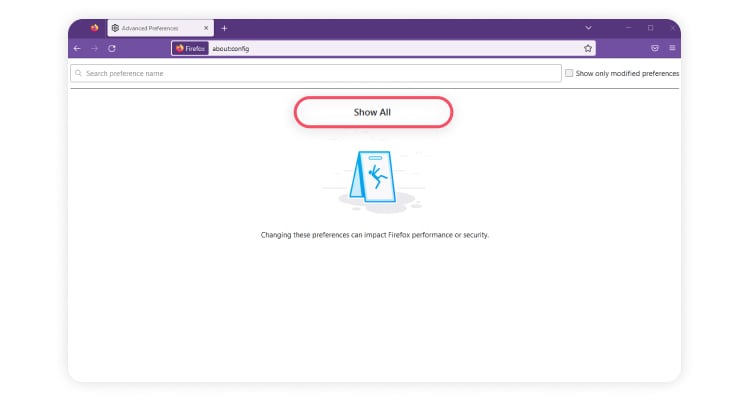
- Click on “Show All.”

- You will be presented with a long list of settings, most of which you probably shouldn’t touch. To find the one you need, type into the search bar at the top of the page: “media.peerconnection.enabled.”

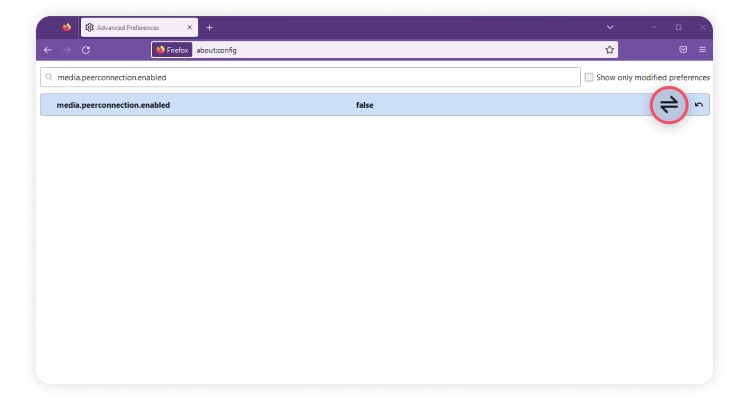
- All you have to do now is press the Toggle button on the far right. The value in the middle of the preference should now display as “False.”

That’s it! This will disable all WebRTC, so it will also disable any websites that use it to deliver their services.
How to disable WebRTC on Safari
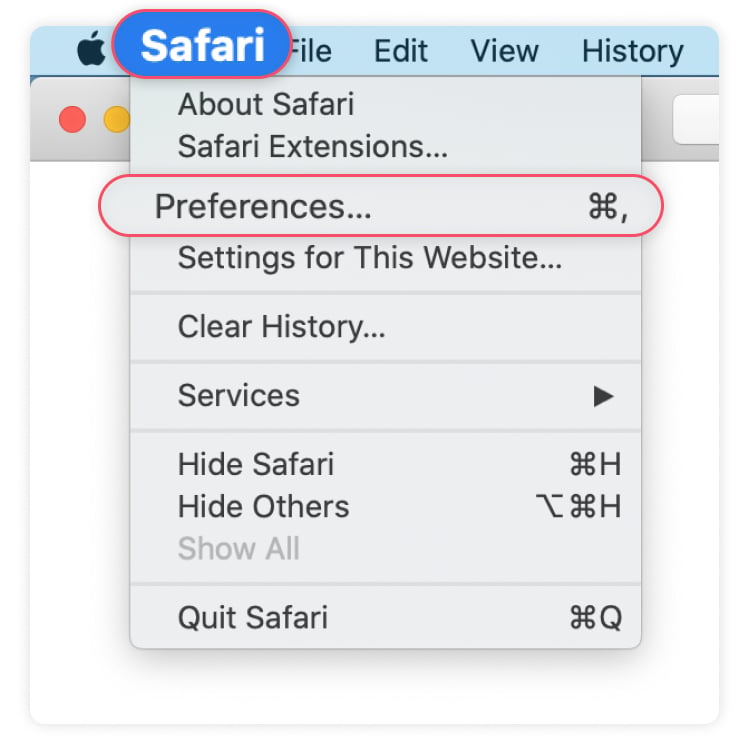
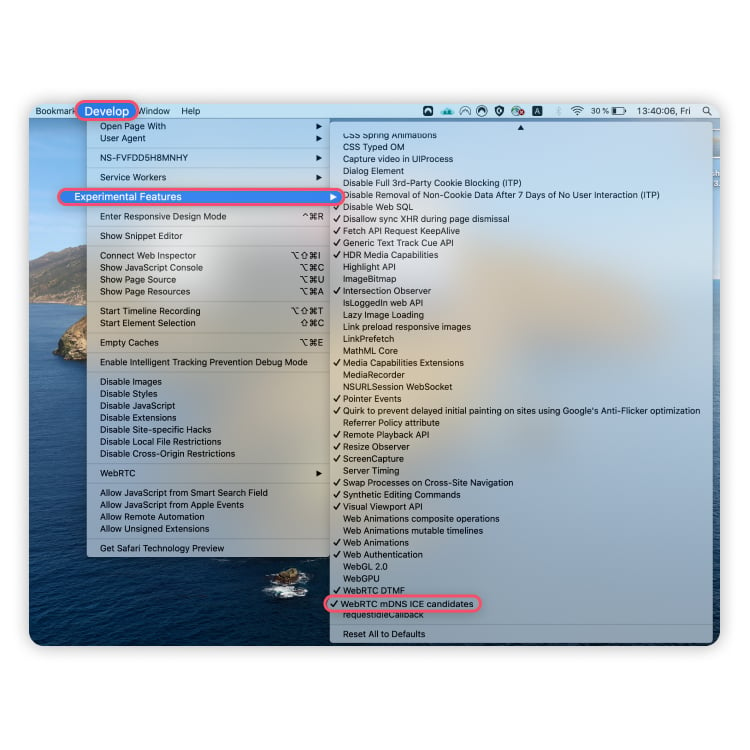
Disabling WebRTC on Safari is possible, but the option is a bit harder to find than on Firefox. That’s because WebRTC was only recently implemented, and is still considered an experimental feature that only developers would want to fiddle with. If you follow these instructions, however, you’ll find it easily!
- Click on “Safari” and choose “Preferences” from the drop-down menu.

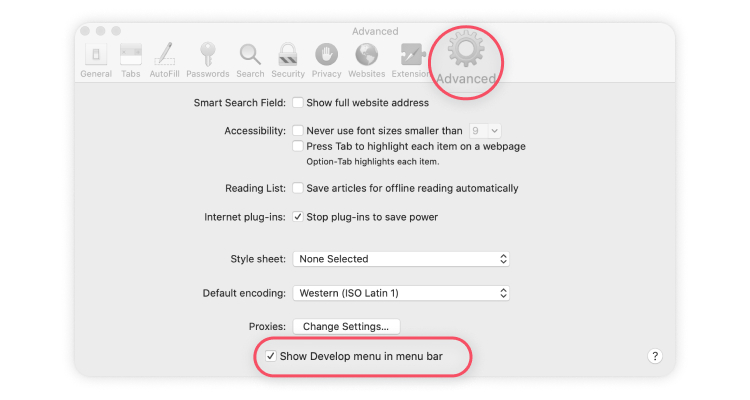
- Click on the “Advanced” tab and check the checkbox that reads “Show Develop menu in menu bar.”

- Click on the new “Develop” tab in the menu bar and choose “Experimental Features” from the drop-down menu. Scroll all the way to the bottom. If “WebRTC mDNS ICE candidates” is checked, click on it to disable it.

That’s it! Your Safari is now free of WebRTC leaks. However, this may also prevent WebRTC-based services from working in your browser.
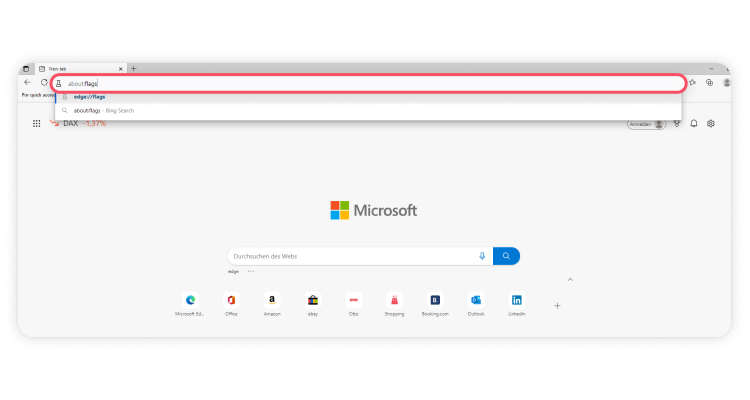
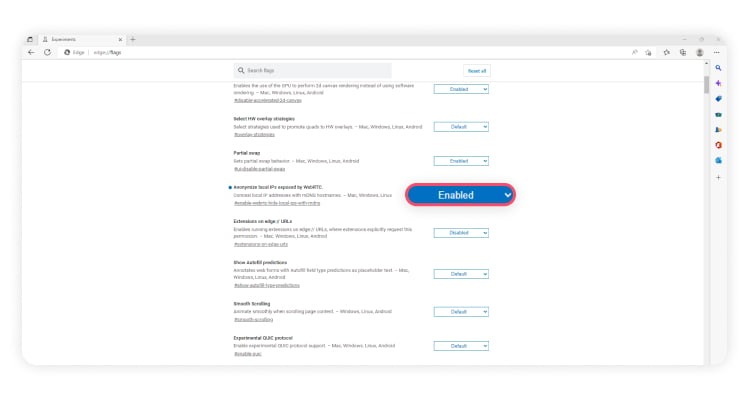
How to disable WebRTC on Microsoft Edge
Disabling WebRTC on Microsoft Edge is easier than disabling it on any other browser. All it takes is two steps.
- Open Edge and type into the address bar: “about:flags.” You’ll be presented with a bunch of settings.

- Scroll to the bottom and find “Hide my local IP address over WebRTC connections”. Make sure the option is turned on. Restart your browser.

That’s it. Simple and easy.
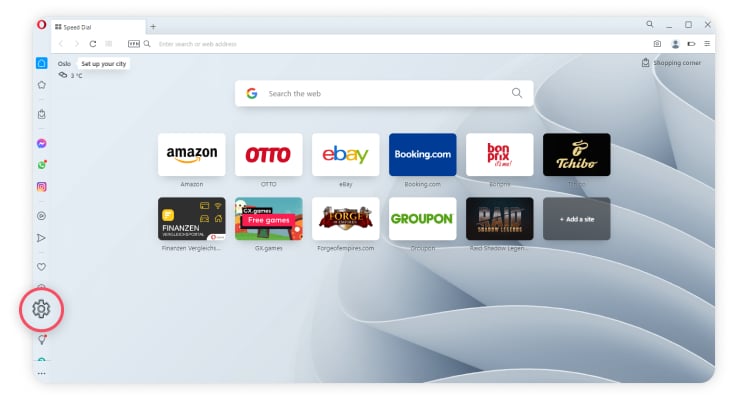
How to disable WebRTC on Opera
Disabling WebRTC on Opera is almost as easy as it is on Microsoft Edge — this time there’s more scrolling.
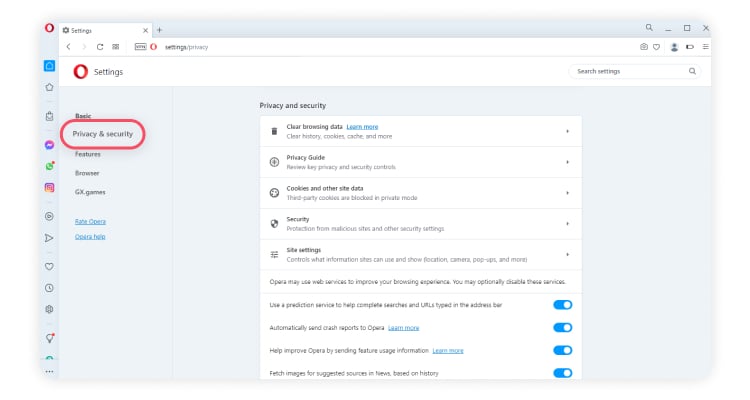
- Open up Opera and delve into the “Settings” located to the left of the window.

- You’ll see an option underneath: “Privacy & security.” Click on it.

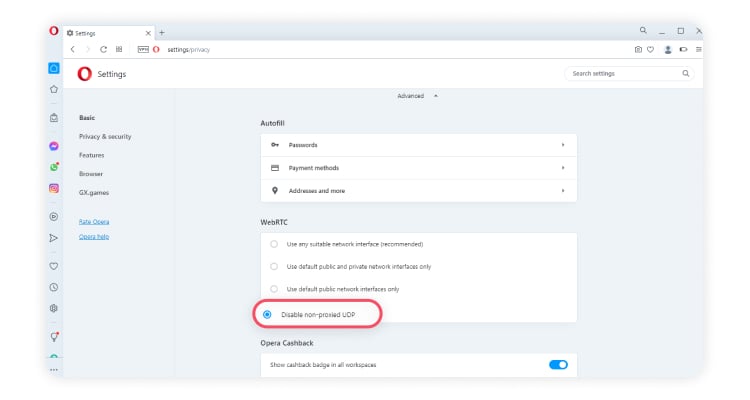
- Scroll down to the section called “WebRTC.” The last option on the list should be “Disable non-proxied UDP.” Make sure it is on. Restart your browser.

Bear in mind that older versions of Opera may not have this option available to them. You may have to explore different options, like a WebRTC control extension.
Blocking WebRTC leaks is not enough
Blocking WebRTC leaks is a good start to securing your online activity, but it’s not enough. If you use NordVPN’s browser extension or VPN service to block these leaks, you’ll already have a collection of tools at your disposal to help you stay secure.
NordVPN offers a variety of useful features, including our Threat Protection system and a Kill Switch to prevent unwanted data exposure. Our premium VPN can give you unrivaled internet speeds, without compromising on strong data encryption.
There’s never been a better time to improve your day-to-day internet safety and protect your privacy. With NordVPN, encryption is just a click away.
NordVPN will keep you secure and private online. Try it with our 30-day money-back guarantee.